What about Azure Policy?!
Hi Blog! Here’s a small explanation about Azure policy and it’s use cases and benefits within the environment. Microsoft Azure…

Hi Blog! Here’s a small explanation about Azure policy and it’s use cases and benefits within the environment. Microsoft Azure…
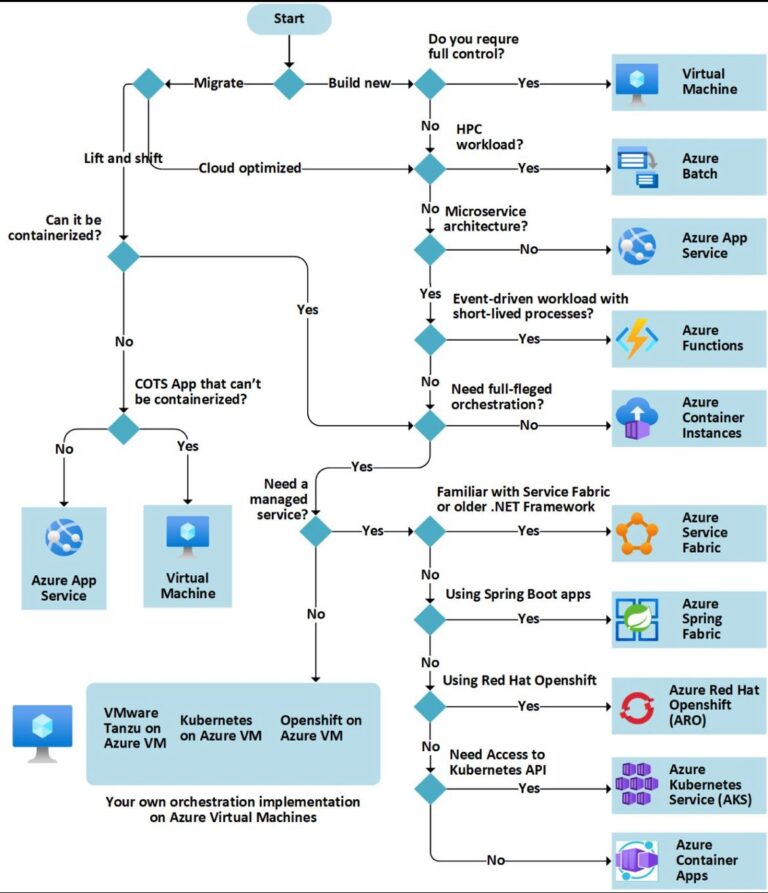
Hey Blog! Here’s some best practices to share about Azure ACI (Azure Container Services) I thought that might be helpful…
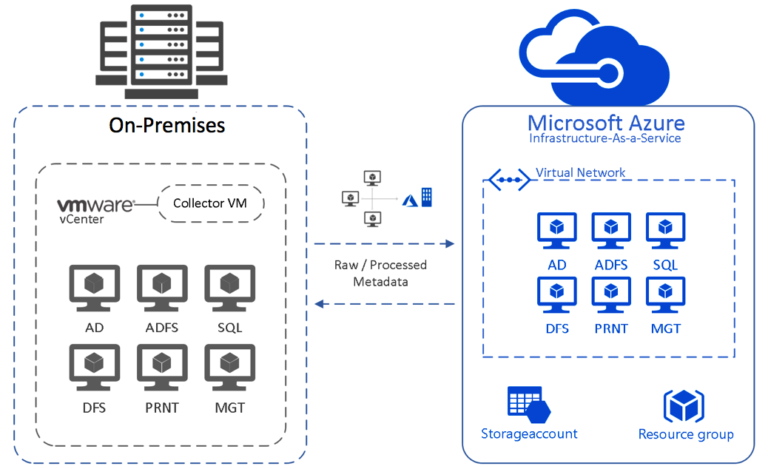
Microsoft Azure is a cloud computing platform that offers a wide range of services to help organizations migrate their workloads…
Hi Blog! Let’s have a quick look at Azure Container Instances or known as Azure ACI. Nowadays, we, in the…
Hello blog! One of the major and important things with cloud technologies is to have a better understanding and DevOps…

Hi blog! We had the chance to have a podcast recording with Azure Developer Community India and that was a…
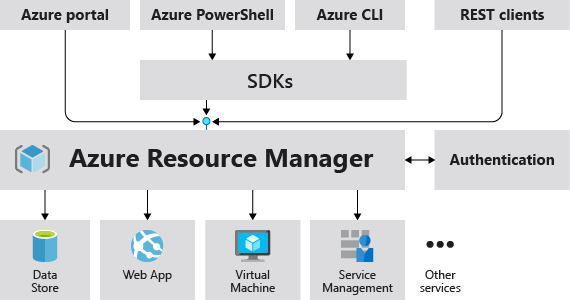
Hello everyone, Here again with another interesting topic called “Azure ARM Templates”. As you know Cloud world is rapidly growing…
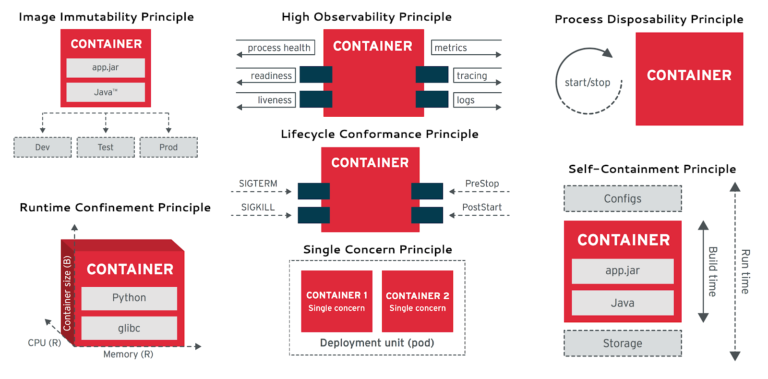
Hello Blog, As you’re away of the Container Based Applications are an important feature in our daily basis tasks and…
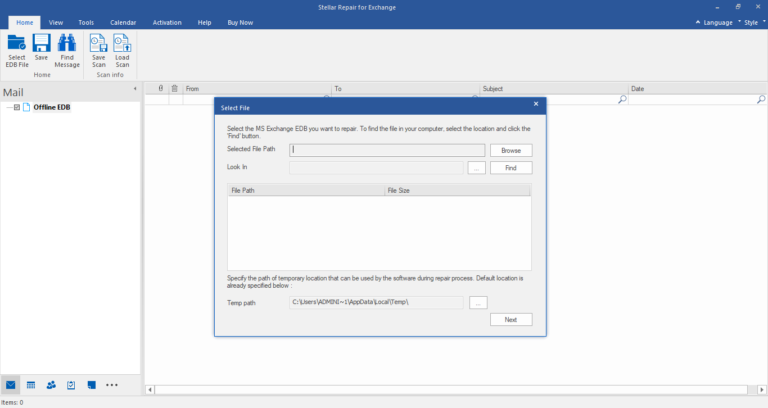
Hello everyone, Today, I’ve got a product to review and write about it – my experience of using Stellar Repair…
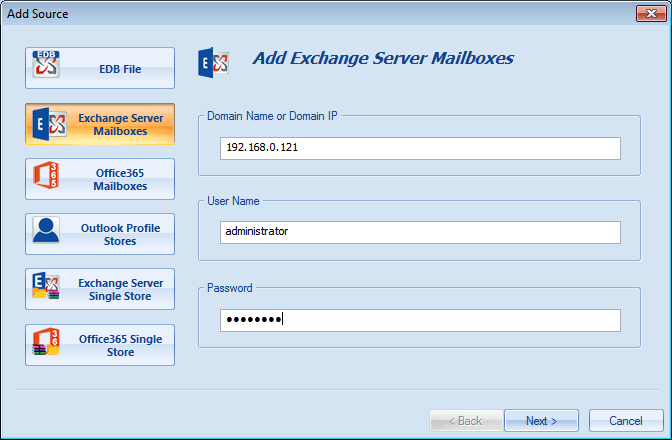
Hello blog, Today I wanted to share my experience of using “Shoviv Exchange Recovery Manager” software, specially for those…
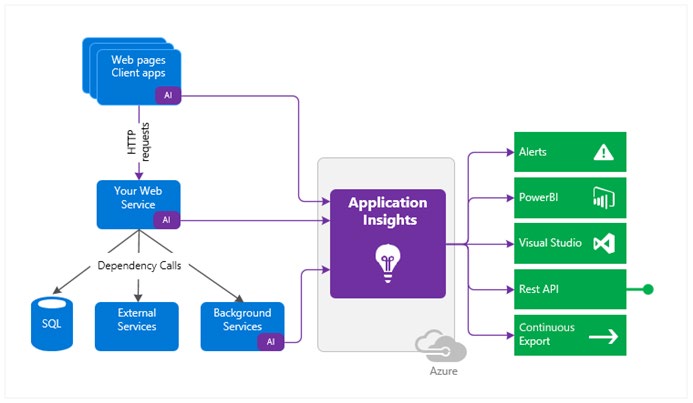
Hello everyone, Today, I’m gonna write a bit about Azure Application Insights which is one of the features of Azure…